104/68 Monday, March 17, 2025
Cybersecurity researchers have uncovered a malicious campaign using fake packages in the Python Package Index (PyPI) to steal sensitive data, including cloud access tokens. According to ReversingLabs, 20 malicious packages were identified in two separate sets, collectively downloaded over 14,100 times before being removed from PyPI. The most downloaded malicious packages include:
- acloud-client (5,496 downloads)
- snapshot-photo (2,448 downloads)
- enumer-iam (1,254 downloads)
- credential-python-sdk (1,155 downloads)
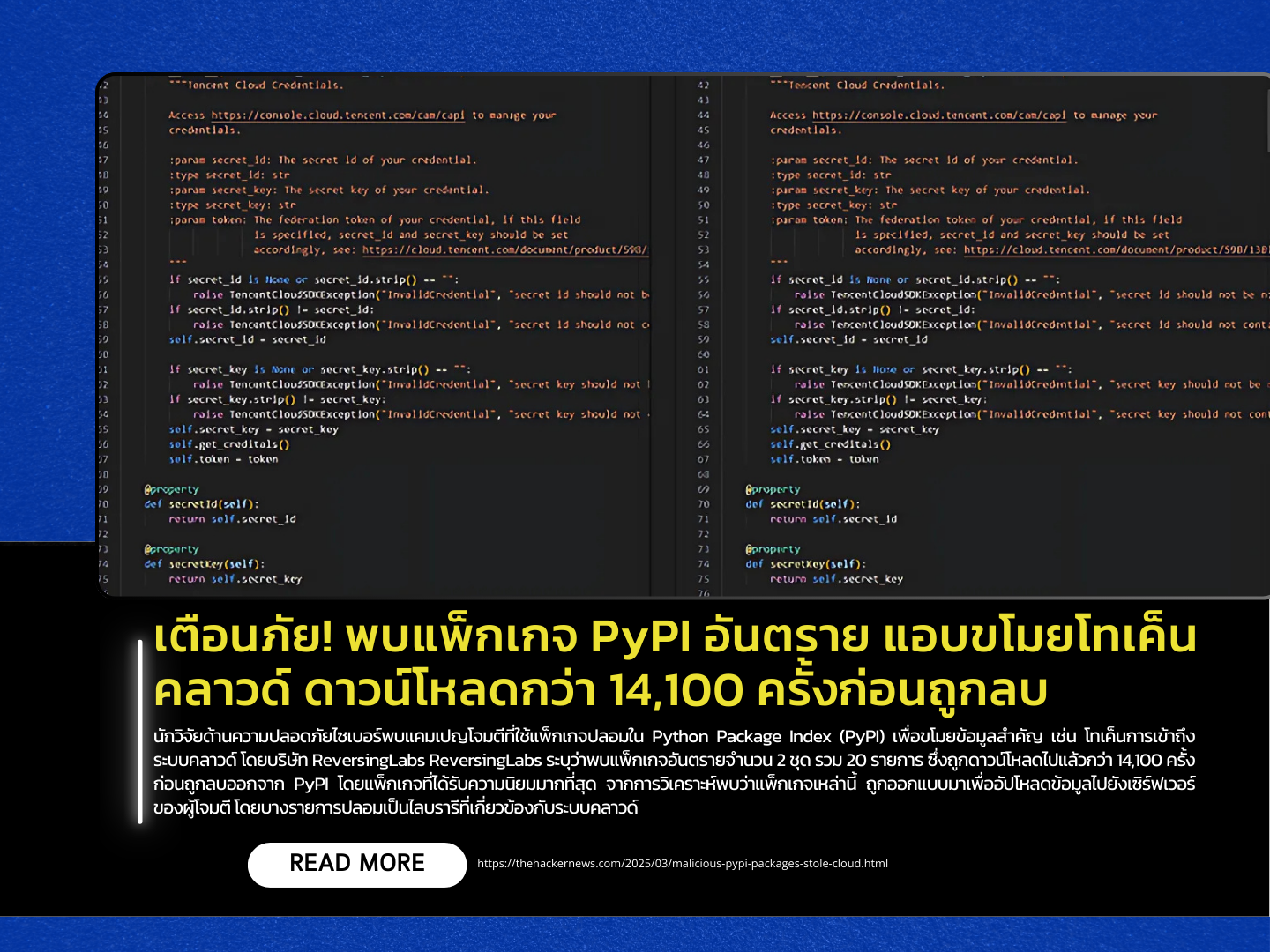
Analysis revealed that these packages were designed to upload stolen data to attacker-controlled servers. Some were disguised as cloud-related libraries, mimicking services like Alibaba Cloud, Amazon Web Services (AWS), and Tencent Cloud. Additionally, some of these malicious packages were dependencies in a popular GitHub project called “accesskey_tools”, potentially exposing unsuspecting users to compromise.
This discovery coincides with a Fortinet FortiGuard Labs report that highlights numerous suspicious packages in PyPI and npm, some of which contain scripts that communicate with command-and-control (C&C) servers or download additional malware. Researchers urge developers to carefully inspect packages before installing and to monitor the URLs associated with these packages to mitigate the risk of cyberattacks.
Source https://thehackernews.com/2025/03/malicious-pypi-packages-stole-cloud.html
