129/68 Thursday, April 3, 2025
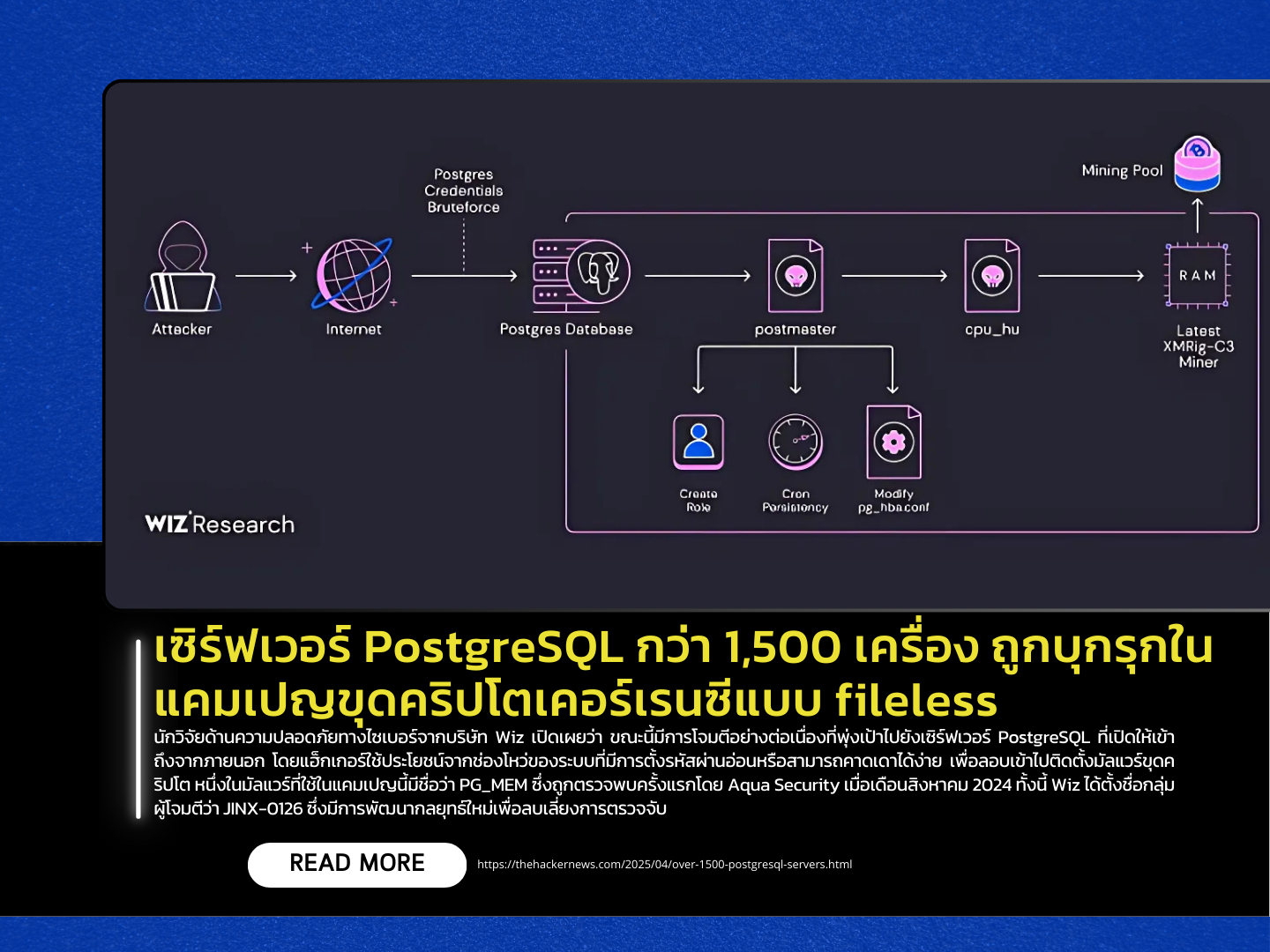
Cybersecurity researchers at Wiz have uncovered an ongoing campaign targeting externally accessible PostgreSQL servers, exploiting weak or easily guessable credentials to deploy fileless cryptocurrency mining malware. One of the key payloads used in this campaign is a malware strain called PG_MEM, which was first detected by Aqua Security in August 2024. Wiz has attributed the activity to a threat actor dubbed JINX-0126, which employs sophisticated evasion tactics such as binary hash randomization for each victim and fileless execution to avoid detection.
A standout technique used in the attacks is the abuse of the SQL command COPY ... FROM PROGRAM, which allows the attacker to execute shell commands directly on compromised servers. After gaining access, the attackers scan the system and deploy a Base64-encoded script designed to eliminate competing crypto miners and install a binary named PG_CORE. They also deploy a Golang-based binary named “postmaster”, which mimics the behavior of a PostgreSQL server, sets up persistence via cron jobs, creates new high-privilege user accounts, and installs another binary named cpu_hu.
The cpu_hu binary fetches and executes the XMRig mining software from GitHub using Linux memfd techniques, enabling fileless crypto mining operations. According to Wiz, the threat actor assigns a unique mining device ID to each infected machine. They identified three cryptocurrency wallets linked to the campaign, each with approximately 550 active mining workers, suggesting that more than 1,500 PostgreSQL servers have been compromised in this large-scale cryptojacking operation.
Source https://thehackernews.com/2025/04/over-1500-postgresql-servers.html
